Ios Swift Trigger Face Id Scan Again Afer User Declines
| Learn SwiftUI and have your iOS Evolution to the Next Level |
In the world of computer security, user authentication falls into the three categories of something you know, something you have and something you are. The "something you know" category typically involves a memorized password or Pivot number and is considered the least secure selection. A more secure choice is the "something you lot accept" approach which usually takes the form of a small authentication token or device which generates 1-fourth dimension access codes on request.
The last category, "something you are", refers to a concrete attribute that is unique to the user. This, of form, involves biometrics in the form of a retina scan, facial or vocalisation recognition or fingerprint.
With the iPhone 5s, Apple introduced a built-in fingerprint scanner which enabled users to access the device and brand purchases in the iTunes, App and iBooks stores using fingerprint authentication. Since the introduction of iOS 8, this biometric authentication capability can at present be built into your own applications. With the introduction of the iPhone X and iOS 11, biometric authentication using facial recognition tin can also be built into your iOS apps.
Contents
The Local Authentication Framework
Biometric authentication for iOS applications is implemented using the Local Authentication Framework. The key course within this framework is the LAContext class which, among other tasks, is used to evaluate the authentication abilities of the device on which the application is running and perform the hallmark.
Checking for Biometric Authentication Availability
Not all iOS devices have the fingerprint scanner or facial recognition and, even on devices with the necessary hardware back up, not all users will have activated these authentication features. The start step in using biometric authentication, therefore, is to check that biometric authentication is a feasible selection on the device:
permit context = LAContext() var error: NSError? if context.canEvaluatePolicy( LAPolicy.DeviceOwnerAuthenticationWithBiometrics, error: &error) { // Biometry is available on the device } else { // Biometry is non available on the device // No hardware support or user has non gear up biometric auth } If biometric authentication is not available, the reason tin be identified by accessing the errorCode holding of the fault parameter and will fall into one of the following categories:
- LAError.biometryNotEnrolled - The user has not enrolled in biometric authentication on the device.
- LAError.passcodeNotSet - The user has not notwithstanding configured a passcode on the device.
- LAError.biometryNotAvailable - The device does not have the required biometric hardware support.
Identifying Authentication Options
In the event that the device on which the app is running contains the necessary biometric hardware, information technology can be useful to place the type of authentication that is supported. This can be achieved by evaluating the biometryType property of the LAContext instance as follows:
permit context = LAContext() var error: NSError? if context.canEvaluatePolicy( LAPolicy.deviceOwnerAuthenticationWithBiometrics, mistake: &error) { if (context.biometryType == LABiometryType.faceID) { // Device support Face ID } else if context.biometryType == LABiometryType.touchID { // Device supports Touch ID } else { // Device has no biometric back up } Evaluating Biometric Policy
In the effect that biometric authentication is available, the side by side stride is to evaluate the policy. This chore is performed past calling the evaluatePolicy method of the LAContext example, passing through the hallmark policy blazon and a message to be displayed to the user. The task is performed asynchronously and a reply closure expression called one time the user has provided input:
context.evaluatePolicy( LAPolicy.deviceOwnerAuthenticationWithBiometrics, localizedReason: "Authentication is required for access", answer: {(success, fault) in // Lawmaking to handle respond hither }) The reply closure expression is passed a Boolean value indicating the success or otherwise of the authentication and an NSError object from which the nature of any failure can be identified via the corresponding error lawmaking. Failure to authenticate will fall into one of the following three categories:
- LAError.systemCancel - The hallmark process was cancelled by the operating organisation. This mistake typically occurs when the application is placed in the groundwork.
- LAError.userCancel - The authentication process was cancelled past the user.
- LAError.userFallback - The user opted to authenticate using a password instead of using Touch or Face ID.
In the event of the user fallback, it is the responsibility of the awarding to prompt for and verify a countersign earlier providing admission.
If the hallmark process is successful, however, the application should provide the user with access to whatever screens, data or functionality were beingness protected.
A Biometric Hallmark Example Project
Launch Xcode and create a new iOS Single View Application project named BiometricID using Swift every bit the programming linguistic communication.
Select the Primary.storyboard file and drag and driblet a Button view then that information technology is positioned in the heart of the storyboard scene. Change the text on the push button so that it reads Authenticate.
With the button selected, brandish the Automobile Layout Marshal menu and configure both horizontal and vertical center in container constraints.
Brandish the Assistant Editor, Ctrl-click on the button view and drag the resulting line to a point beneath the ViewController class declaration line. On releasing the line, establish a connection to an outlet named authButton.
Finally, Ctrl-click and drag from the button view to a position merely beneath the viewDidLoad method in the ViewController.swift file. Release the line and, in the connection dialog, establish an Action connexion to a method named authenticateUser.
On completion of the user interface blueprint the layout should resemble Figure 63-1:
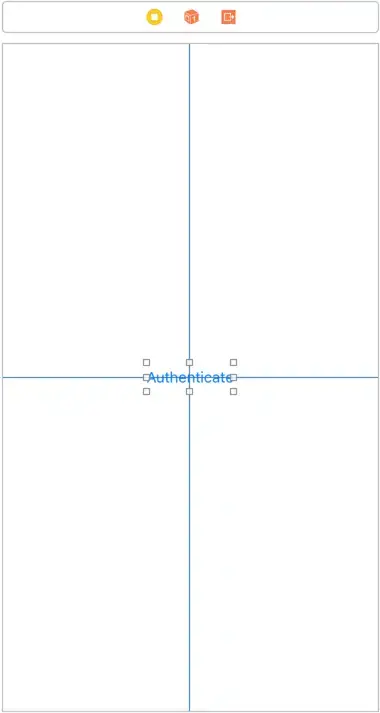
Effigy 63-i
Checking for Biometric Availability
With the user interface designed, the side by side step is to add some code to the authenticateUser method to verify that the device can handle biometric authentication. Select the ViewController.swift file, import the LocalAuthentication Framework and add together code to the authenticateUser method as follows:
import UIKit import LocalAuthentication course ViewController: UIViewController { override func viewDidLoad() { super.viewDidLoad() // Exercise any additional setup after loading the view, typically from a bill. } @IBAction func authenticateUser(_ sender: Any) { let context = LAContext() var error: NSError? if context.canEvaluatePolicy( LAPolicy.deviceOwnerAuthenticationWithBiometrics, mistake: &error) { // Device tin can use biometric hallmark } else { // Device cannot use biometric authentication if let err = error { switch err.code{ case LAError.Code.biometryNotEnrolled.rawValue: notifyUser("User is non enrolled", err: err.localizedDescription) case LAError.Lawmaking.passcodeNotSet.rawValue: notifyUser("A passcode has non been fix", err: err.localizedDescription) instance LAError.Code.biometryNotAvailable.rawValue: notifyUser("Biometric authentication not available", err: err.localizedDescription) default: notifyUser("Unknown mistake", err: err.localizedDescription) } } } } In add-on to evaluating hallmark policy, the higher up code too identifies whether the device supports Face ID or Touch ID authentication and updates the text displayed on the authButton instance accordingly.
| Learn SwiftUI and take your iOS Development to the Side by side Level |
Before proceeding, implement the notifyUser method as follows:
func notifyUser(_ msg: String, err: String?) { permit alert = UIAlertController(championship: msg, message: err, preferredStyle: .alert) permit cancelAction = UIAlertAction(title: "OK", style: .cancel, handler: nil) alert.addAction(cancelAction) cocky.present(warning, blithe: true, completion: cypher) } Seeking Biometric Authentication
The side by side task is to attempt to obtain authentication from the user. This involves a call to the evaluatePolicy method of the local authentication context:
@IBAction func authenticateUser(_ sender: Whatever) { let context = LAContext() var error: NSError? if context.canEvaluatePolicy( LAPolicy.deviceOwnerAuthenticationWithBiometrics, error: &error) { // Device tin use biometric authentication context.evaluatePolicy( LAPolicy.deviceOwnerAuthenticationWithBiometrics, localizedReason: "Access requires authentication", reply: {(success, error) in DispatchQueue.main.async { if allow err = fault { switch err._code { example LAError.Code.systemCancel.rawValue: cocky.notifyUser("Session cancelled", err: err.localizedDescription) case LAError.Lawmaking.userCancel.rawValue: self.notifyUser("Delight effort again", err: err.localizedDescription) case LAError.Code.userFallback.rawValue: self.notifyUser("Hallmark", err: "Password choice selected") // Custom code to obtain password here default: self.notifyUser("Authentication failed", err: err.localizedDescription) } } else { self.notifyUser("Authentication Successful", err: "You now have full access") } } }) } else { // Device cannot use biometric authentication if permit err = fault { switch err.code { example LAError.Lawmaking.biometryNotEnrolled.rawValue: notifyUser("User is not enrolled", err: err.localizedDescription) case LAError.Code.passcodeNotSet.rawValue: notifyUser("A passcode has non been set up", err: err.localizedDescription) case LAError.Lawmaking.biometryNotAvailable.rawValue: notifyUser("Biometric authentication not available", err: err.localizedDescription) default: notifyUser("Unknown error", err: err.localizedDescription) } } } } | Larn SwiftUI and accept your iOS Development to the Adjacent Level |
The code added to the method initiates the authentication process and displays a bulletin confirming a successful authentication. In the event of an authentication failure, a message is displayed to the user indicating the reason for the failure. Pick of the password option simply confirms that the option was selected. The actual action taken in this state of affairs will be application specific but will likely involve prompting for a password and verifying it confronting a database of valid passwords.
Adding the Face up ID Privacy Statement
The final step before testing is to configure the Face ID privacy statement within the projection's Info.plist file. This is the statement that is displayed to the user when the app seeks permission to use Confront ID authentication. To add this entry, select the Info.plist file in the projection navigator panel and click on the + push button located in the bottom entry of the list. From the resulting menu, select the Privacy - Face ID Usage Description option and enter a description into the value field:
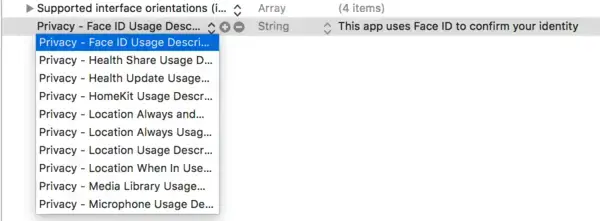
Effigy 63-2
Testing the Awarding
Biometric authentication can be tested either on physical iOS devices that include biometric support, or using the simulator surround.
When testing Confront ID support on a simulator, compile and run the app on an iPhone 10 simulator. Once the app has launched, select the simulator'southward Hardware -> Face ID bill of fare and brand certain the Enrolled pick is enabled (equally highlighted in Effigy 63 iii) before borer the Cosign push button within the app.
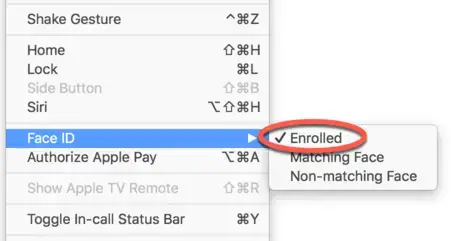
Figure 63-3
At this bespeak, the Face ID permission asking dialog will appear displaying the privacy statement that was previously entered into the Info.plist file equally shown in Effigy 63-4:
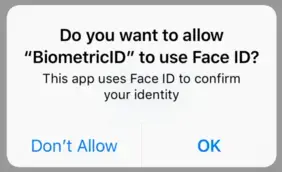
Figure 63-four
After granting permission by clicking on the OK button, the gray simulated Face ID panel (Effigy 63-5) should appear:
Figure 63-5
To simulate a matching face, select the Hardware -> Face ID -> Matching Confront menu option afterwards which the app should display the dialog shown in Figure 63-6 indicating that the authentication was successful:
Effigy 63-6
Echo the authentication process, this time selecting the Non-matching menu option and verify that the hallmark fails.
Launch the app on a physical device with Touch ID support, or use a suitable simulator example (for instance an iPhone viii) to test Bear upon ID authentication. If using a simulator, brand sure that the Hardware -> Touch on ID -> Enrolled choice is enabled before clicking the Authenticate button. When instructed to touch the dwelling push, select the Hardware -> Bear on ID -> Matching Touch carte option to test the authentication. After a successful hallmark, try once more using the Not-matching Bear upon option.
Summary
Introduced with iOS 7 and the iPhone 5s device, Touch ID has been provided to iOS users as a way to gain access to devices and to make Apple related purchases. Since the introduction of iOS viii, fingerprint hallmark using the Touch ID system has been available to application developers. With the introduction of iOS 11 running on the iPhone Ten, hallmark support has been extended to include facial recognition. This affiliate has outlined the steps involved in using the Local Hallmark Framework to implement biometric hallmark using both the Touch ID and Face ID systems.
gilmartinowly1981.blogspot.com
Source: https://www.techotopia.com/index.php/Implementing_TouchID_Authentication_in_iOS_8_Apps



0 Response to "Ios Swift Trigger Face Id Scan Again Afer User Declines"
Postar um comentário